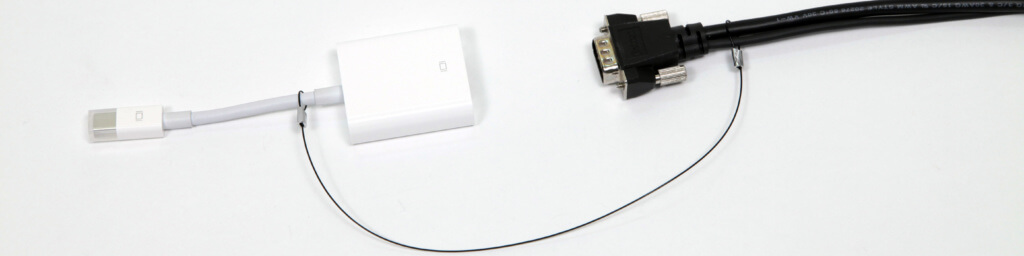
As you’re considering whether TetherTies™ are the right computer peripheral security tool for your organization, we wanted share the simple 4 step installation instructions below. TetherTies come fully assembled, and require only a simple crimp to secure to the TetherTie in place. There’s no need to assemble the TetherTie, nor any need to heat shrink […]
4 Simple Steps to Install TetherTies in 15 Seconds or Less